SharePoint external sharing governance helps organizations collaborate with clients, vendors, partners, and outside stakeholders without letting guest access, Anyone links, direct sharing, and site-level exceptions become unmanaged risk. This article explains how external sharing should be controlled, reviewed, and aligned with permissions, lifecycle governance, compliance, and Copilot readiness.
External sharing in SharePoint is easy to enable. Running it well takes more discipline.
That is where many organizations get into trouble. Files are shared too broadly. Site owners make different judgment calls. Leadership assumes controls are tighter than they actually are. Over time, practical collaboration can turn into a governance issue, a compliance concern, and, in some environments, a Copilot readiness problem.
The point is not to block collaboration. The point is to make external collaboration intentional, controlled, and easier to trust.
This article focuses specifically on external sharing decisions: guest access, Anyone links, direct file sharing, site-level sharing rules, owner accountability, link expiration, and access review. For the broader governance model, start with The Complete Guide to SharePoint Governance for Microsoft 365. For the underlying access model, use The Complete Guide to SharePoint Permissions. When sensitive content is involved, SharePoint sensitivity labels can help define whether the workspace, the file, or both need stronger protection.
What this article covers
This article explains:
- What SharePoint external sharing governance should include
- Why guest access, Anyone links, direct sharing, and site-level rules need clear ownership
- How unmanaged external sharing creates permissions, compliance, lifecycle, and trust issues
- How external sharing affects search, sensitive content exposure, records, and Copilot readiness
- When external sharing concerns should become an access review, governance cleanup, sensitivity label planning effort, advisory discussion, or larger SharePoint security project
What SharePoint external sharing governance really means
SharePoint external sharing governance is the operating model behind how your organization shares content with people outside the business.
That includes:
- Guest access
- Sharing links
- Site-level sharing rules
- File and folder sharing behavior
- Ownership and review expectations
- Link expiration and access cleanup
- Oversharing prevention
- Alignment with compliance and Copilot readiness goals
Many organizations treat external sharing like a simple admin setting. That view is too narrow.
A stronger approach treats external sharing as a business control. It affects security, user behavior, client collaboration, records exposure, and long-term platform trust.
This is where environments start to drift. The platform supports collaboration. The organization never fully defines the rules around it.
Why external sharing becomes a problem so quickly
External sharing usually breaks down for a few predictable reasons.
In many cases, the organization enables sharing but never clearly defines where it should happen. Teams start sharing from communication sites, project sites, personal OneDrive folders, and ad hoc workspaces without a consistent model.
Site owners are then given responsibility without enough guardrails. Most make reasonable decisions in the moment, but those decisions vary from site to site.
Link sharing often fills the policy gap. Instead of following a governed guest access model, users rely on whichever option feels fastest.
Over time, access stops getting reviewed. Files that were appropriate to share six months ago may no longer be appropriate today.
This is one of the most common SharePoint governance mistakes we see. Organizations focus on whether external sharing is enabled. Much less time gets spent defining how it should be used.
That is backwards.
The better question is not, “Can we share externally?” A better question is, “What external sharing model can we manage with confidence?”
External sharing is not just a permissions issue
It is easy to frame external sharing as a permissions topic. Permissions matter, but they are only part of the picture.
External sharing also touches:
- Information architecture
- Site purpose
- Ownership maturity
- Retention expectations
- Client confidentiality
- Search visibility
- Lifecycle governance
- Copilot exposure risk
When external collaboration includes confidential documents, SharePoint sensitivity labels can help define whether the workspace, the file, or both need stronger protection before guests are invited.
For that reason, this topic should sit close to your broader governance model, not off to the side as a one-time admin task.
Organizations that already struggle with broken inheritance, unclear site ownership, or weak content lifecycle rules usually struggle with external sharing too. In many cases, the same structural issues that show up in a weak sharing model also show up in broader permission sprawl, which is why a page like the SharePoint Permissions Guide often becomes relevant long before external sharing is reviewed formally.
For the broader model around permissions, lifecycle, records, site provisioning, search, and AI readiness, the SharePoint governance cluster map shows where external sharing governance fits in the full dataBridge governance resource set.
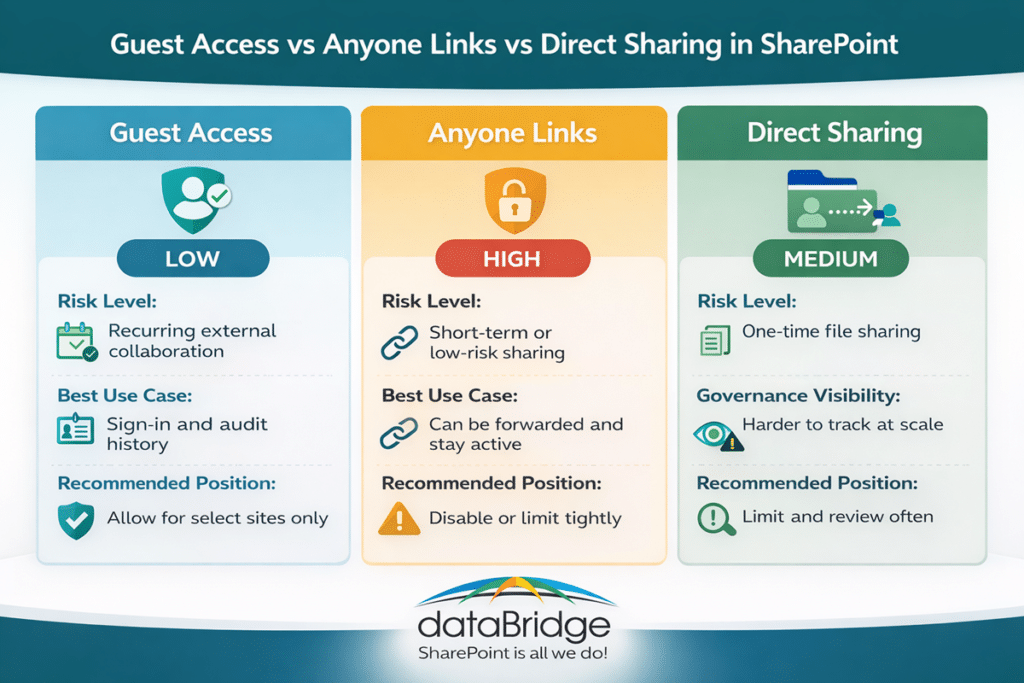
Guest access, Anyone links, and direct sharing are not the same
This is where many users, and even some administrators, get tripped up. Not all external sharing methods create the same level of risk.
Guest access
Guest access is usually the most governable model when external collaboration is legitimate and ongoing.
A guest signs in with an authenticated identity. That makes access easier to trace and easier to manage over time.
This model works well when vendors, partners, consultants, or clients need recurring access to a defined site, Team, or shared workspace.
Guest access is not risk free. Even so, it is usually far easier to govern than anonymous sharing.
Anyone links
Anyone links are convenient. They are also one of the easiest ways to create oversharing.
These links can be forwarded. Accountability drops. In many environments, the link outlives the business need unless someone actively manages expiration and cleanup.
In our experience, Anyone links are often used because the governed option feels slower or less clear.
That is usually a process problem, not just a user problem.
Direct file or folder sharing
Direct sharing often feels harmless. One person shares one file with one external contact and moves on.
At scale, that creates a visibility problem. Important external access becomes scattered across libraries, folders, and individual documents. Governance turns reactive because no one is working from a clean operating model.
This is one reason strong site design matters. Better structure reduces the need for one-off sharing in the first place. It also helps teams make better platform decisions earlier, especially when they understand the practical differences covered in OneDrive vs SharePoint.
The real risk is inconsistency
Most external sharing problems do not come from one dramatic mistake.
They come from hundreds of smaller inconsistencies.
One site allows broad sharing. Another site is tightly controlled. One owner understands the rules. Another owner does not. One team reviews access quarterly. Another team never reviews it at all.
That inconsistency weakens trust.
It also makes support harder. IT ends up troubleshooting exceptions instead of enforcing a model.
This is where governance has to become practical. A policy document alone will not fix the issue. Site owners need clear rules, realistic defaults, and defined escalation paths.
External Sharing Governance Decision Table
Sharing scenario | Recommended model | Governance requirement |
Ongoing client or partner collaboration | Authenticated guest access | Named owner, defined site, scheduled review |
One-time low-risk file sharing | Direct sharing, if allowed | Expiration and business justification |
Broad anonymous distribution | Avoid or tightly restrict Anyone links | Clear policy exception and expiration |
Sensitive or regulated content | Restricted sharing model | Compliance or security review |
Project collaboration with external users | External collaboration site | Template, owner, guest review, lifecycle path |
How Copilot changes the external sharing conversation
Copilot did not create oversharing. It did make more organizations pay attention to it.
That is a healthy shift.
When leadership starts preparing for Microsoft 365 Copilot, many teams realize the real issue is not AI itself. The real issue is that content access has been loosely governed for years.
Copilot increases visibility into content people already have access to. Because of that, weak external sharing practices deserve more scrutiny now, not less.
This does not mean every shared file becomes a crisis. It does mean organizations should stop treating external access as a background setting.
When external sharing is loosely managed, content boundaries become harder to explain and harder to defend. In an AI-enabled environment, that matters more. That is one reason organizations working through external sharing questions often end up looking at broader controls like those discussed in SharePoint Advanced Management for Copilot.
At dataBridge, we often tell clients the same thing: Copilot readiness is rarely just about Copilot. More often, it exposes governance debt that was already there.
That is why external sharing governance should be part of the broader readiness conversation alongside permissions, content quality, ownership, and lifecycle controls.
When guest access or open sharing links are part of the concern, download the SharePoint Permission Review Checklist for Copilot to review external users, link types, site owners, and high-risk content before Copilot expands.
Signs your external sharing model needs work
Many organizations already know something is off. They just have not named the problem clearly yet.
Here are some common warning signs:
- Site owners are unsure when external sharing is allowed
- Anyone links are used because they are the fastest option
- Teams and SharePoint are both being used without clear rules
- Sensitive documents live in broadly accessible locations
- Guest users are not reviewed on a regular schedule
- Project workspaces remain open long after the project ends
- External access decisions vary by department
- Leadership wants Copilot, but governance confidence is low
If several of these sound familiar, the issue is probably not user behavior alone. In most cases, the bigger problem is that the organization has not made the right behavior clear and repeatable.
A better governance model for SharePoint external sharing
The strongest external sharing models are not built around fear. They are built around clarity.
That means defining the right control points before users create workarounds.
1. Set organization-level rules first
Start with the broadest boundaries.
Decide whether external sharing is allowed at all, where it is allowed, and which sharing methods fit your risk tolerance. Those decisions should not be left to informal habits.
An organization-level model creates consistency. It also keeps every department from inventing its own version of the rules.
2. Define which site types can support external sharing
Not every site should allow external sharing.
Project sites, client collaboration spaces, and selected team workspaces may support it. Broad intranet areas, sensitive operational sites, and records-heavy locations often should not.
This is one reason architecture matters so much. External sharing becomes easier to govern when site purpose is clear. External sharing is also easier to control when new workspaces follow a model for controlled SharePoint site provisioning that defines which site types can support external access, who owns sharing decisions, and how those sites should be reviewed over time.
Strong SharePoint environments do not treat every site the same. They set different governance expectations by site type, which is also a core planning issue in SharePoint Strategy & Roadmapping.
3. Make authenticated guest access the default where possible
When external collaboration is legitimate and ongoing, authenticated guest access is usually easier to govern than anonymous sharing.
It creates more accountability. It also fits better with repeat collaboration, ownership review, and access management.
This does not mean every external scenario needs a guest account. It does mean convenience should not be the only factor driving the decision.
4. Restrict or tightly control Anyone links
Anyone links should be treated carefully.
In many organizations, they should be disabled or limited to narrow use cases. In others, they may remain available with expiration controls and clear guidance.
The key is to decide intentionally. Anyone links should never become the default simply because no one defined a better model.
5. Assign owner accountability
External sharing cannot be governed only from the admin center.
Site owners need to understand what kind of content belongs in their site, when external access is appropriate, and how to review that access over time.
This is where governance often fails in practice. Technical controls exist, but owner accountability stays vague.
That gap creates long-term risk.
6. Build a review cadence
External access should be reviewed on a schedule.
Quarterly reviews work well for many organizations. Higher-risk environments may need a tighter cycle. Lower-risk workspaces may not.
What matters most is that the review is real. A governance model without a review habit will eventually drift.
7. Tie sharing decisions to site lifecycle
Temporary collaboration spaces should not stay open forever.
Projects end. Vendor relationships change. Client work wraps up. External access should follow that lifecycle.
This is where external sharing governance becomes much stronger when it connects to provisioning, ownership, and site retirement practices.
SharePoint, OneDrive, and Teams each need a role
External sharing gets messier when organizations use Microsoft 365 without clear platform boundaries.
That is why dataBridge often recommends a simple rule: define what belongs where before trying to govern how it is shared.
SharePoint usually fits structured team or project collaboration. OneDrive often fits individual draft work and limited person-to-person sharing. Teams adds conversation and workspace context, but it still relies heavily on SharePoint behind the scenes.
When those roles are blurred, external sharing becomes harder to control.
A file may start in OneDrive, move into a Team, then get copied into a project site with different permissions and no clear ownership path. That is how governance debt grows. Organizations that need to clean up those boundaries often start with OneDrive vs SharePoint and then extend the conversation into workspace governance through Microsoft Teams Consulting Services.
What good external sharing governance looks like in practice
A well-governed model is usually less dramatic than people expect.
It does not block every collaboration scenario. It does not force users through unnecessary friction. It makes the right path clear.
In a mature model:
- Approved site types support external sharing
- Guest access is preferred for ongoing collaboration
- Anyone links are restricted or intentionally limited
- Site owners understand their responsibilities
- Access is reviewed on a schedule
- Temporary workspaces have lifecycle controls
- High-risk content is handled differently
- Governance and Copilot readiness support each other
That is what sustainable control looks like.
It is not flashy. It is effective.
A short real-world pattern we see often
A client wants faster collaboration with outside partners. External sharing is enabled quickly because the business need is real.
At first, the setup works. Teams move faster. Files are easier to exchange. People feel productive.
Then the exceptions begin.
Different departments use different approaches. Some rely on guest access. Others send Anyone links. A few store client files in places that were never designed for long-term shared collaboration.
Months later, leadership starts asking Copilot readiness questions. Suddenly, the organization is not just reviewing AI. It is reviewing years of sharing behavior, unclear boundaries, and weak owner accountability.
That is a common pattern.
The lesson is simple: external sharing works best when governance is built in early. Retrofitting control later is always harder.
When to get outside help
Some organizations can tighten external sharing rules on their own.
Others need help because the issue is bigger than settings.
That usually happens when:
- Site ownership is inconsistent
- Teams and SharePoint boundaries are unclear
- Sensitive content is spread across many workspaces
- Governance policies exist but are not operationalized
- Leadership wants Copilot readiness without slowing collaboration
- No one is confident that the current model is defensible
That is where outside guidance becomes valuable. The right consulting support helps you define a model that matches how your business actually works, not just how the admin center is configured. If you want help reviewing guest access, sharing links, site-level controls, and broader Microsoft 365 governance, contact dataBridge.
Final thoughts
External sharing is not the problem. Weak governance is the problem.
Most organizations do not need to eliminate external collaboration. They need to govern it with more precision.
That starts by defining where external sharing belongs, which methods are acceptable, who owns the decision, and how access gets reviewed over time.
It also means treating oversharing as a business risk before Copilot or any other AI tool makes that risk more visible.
At dataBridge, we have found that the best SharePoint environments are not the ones with the most restrictive rules. They are the ones with the clearest operating model.
That is what external sharing governance should deliver.
If your organization wants a more defensible approach to SharePoint, Teams, OneDrive, and Copilot readiness, contact dataBridge.